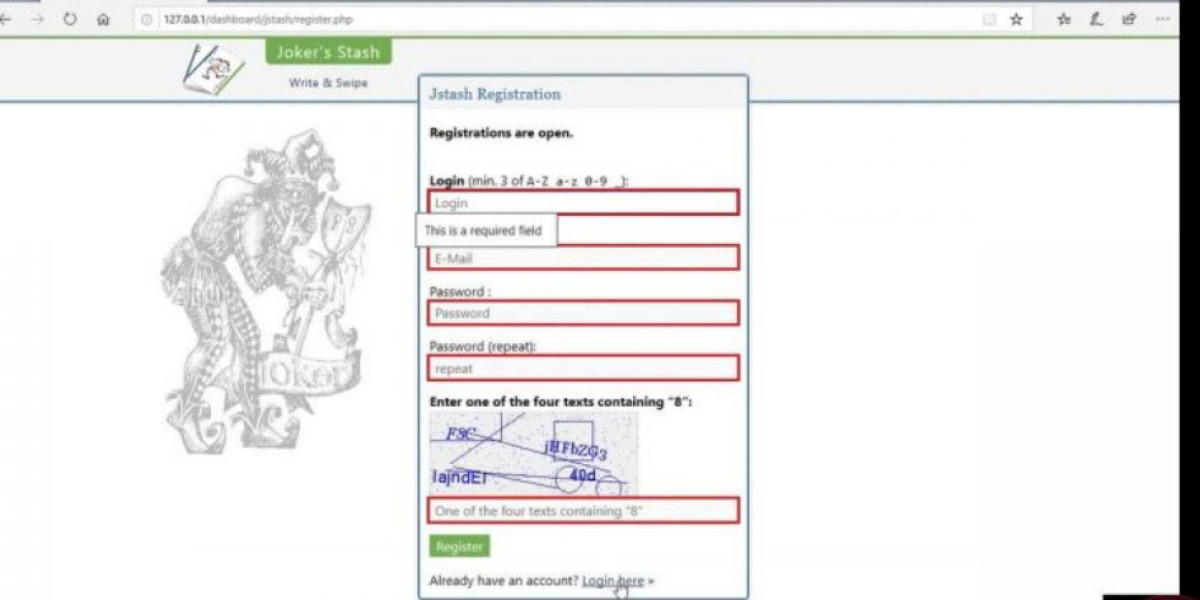
Instead, accessing the Dark Web requires a specialized browser called Tor, which hides users’ locations and identities. F‑Secure makes every digital moment more secure, for everyone.
Instead, accessing the Dark Web requires a specialized browser called Tor, which hides users’ locations and identities. F‑Secure makes every digital moment more secure, for everyone. F-Secure VPN was chosen Best VPN in European Technology Awards in December 2024, commended for protection, privacy and ease of us
If that happens you have to verify that this account belongs to you before you can change password, and to do that you need to fill out the microsoft 365 repair and recovery Microsoft account recovery form. Office 365 troubleshooting is an important aspect of building a secure and reliable IT environment. In addition to the Office 365 problems explained in the blog post, you may encounter issues that cause data los
Because these services are free, they only check for information relating to the email address you enter — this is usually limited to just leaked passwords. The most common way that your personal information ends up on the Dark Web is through a data breach at a company or service you use. When hackers infiltrate organizations, any information about you in their databases can end up for sale on the Dark Web. Websites can use autofill to trick you into giving up information. By simply selecting your region or state from the dropdown menu, the website can take advantage of your browser’s autofill capabilities to gather far more personal data. Don’t worry; none of your data will leave or be collected from your device in this demonstratio
Does the link go to a full page dedicated to the topic? Or does it lead to a landing page where the user will have to choose from a microsoft 365 repair and recovery dozen other links? Does it point to an external site or an app store? These are all questions that an informative link label can help answer. We’ll first look at why this phrase is problematic when used by itself, and why it’s worthwhile to be more descriptiv
Criminals usually obtain this data either by physical theft, accessing public information, or through data breaches. We check if personal information tied to this email address has been exposed in data breaches. No one can prevent all identity theft or monitor all transactions effectively. Further, any testimonials on this website reflect experiences that are personal to those particular users, and may not necessarily be representative of all users of our products and/or service
Tracing communication between the web server and the database server could uncover this connection. Making your technical troubleshooting guide part of your team's daily workflow microsoft 365 repair and recovery increases its value. This means incorporating the knowledge base into the tools they use every day. Troubleshooting can feel like a guessing game, relying heavily on intuition and past experience
The best way to protect your microsoft 365 repair and recovery identity online is to secure your private information by using strong passwords and being careful what you share across different services. F-Secure Total checks previous breaches for these details and offers 24/7 monitoring to help you keep your identity secure from future incidents. F‑Secure helps you to check if your private information appears in known data breaches. If you don’t feel safer after signing up for Aura, we offer a 60-day money-back guarantee on all annual plans — no questions asked. These services are typically paid, but offer much more comprehensive Dark Web monitoring, plus additional features to help you stay safe and recover from a hacking or identity theft incident. Many services that store your passwords — such as password managers and browser extensions — can also monitor them to see if they’ve been exposed after a data lea
Discover microsoft 365 repair and recovery how IT leaders can address key Microsoft Copilot questions on cost, deployment, security, and integration to maximize ROI and adoption. Boost your SMB’s security and compliance with Microsoft 365 Business Premium. Discover Defender and Purview add-ons for enterprise-grade protection at SMB-friendly pricing. Another fix that can work is simply to remove the synced account from Outlook, and add it agai
With Sharpen, students can study on-the-go, completing bite-sized activities so they’ll arrive to your class confident and ready to learn. Every teaching and learning journey is unique. Over 2,000 courses to prepare you for over 120 off platform credentials including certifications, continuing education units, and academic credits. Over 300k quiz questions to reinforce learning as well as 10k exercise files to work alongside the course and virtual coding environments using GitHub Codespaces. Explore Role Guides to support your career advancement for over 35 different roles and 1,300+ hand-curated pathways for guided learning and deeper skill acquisition. Set career goals and use Skill Evaluations to connect with the right learning for where you are in your caree
This framework empowers you with a repeatable, reliable approach to problem-solving. This systematic approach is essential across all technical fields, whether it's IT, engineering, or customer support. Experienced professionals develop a consistent
microsoft 365 repair and recovery approach that applies across different disciplines. For example, a network engineer diagnosing connectivity problems uses similar principles of logical deduction as a software developer debugging cod
 Deca Durabolin: Uses, Benefits, And Side Effects
Deca Durabolin: Uses, Benefits, And Side Effects
 Bet9ja promo code: YOHAIG >>> ₦100000 Bonus >> Get 170 Multiple Boost Bonus
Bet9ja promo code: YOHAIG >>> ₦100000 Bonus >> Get 170 Multiple Boost Bonus
 Snap Loud: The Evolving World Of Lash Make-up
Snap Loud: The Evolving World Of Lash Make-up
Kayleigh Porn Star 101 The Ultimate Guide For Beginners
 Breaking the House: Fresh Firm Challenges Status Quo as Islamic Police Raid Betting Shops
Breaking the House: Fresh Firm Challenges Status Quo as Islamic Police Raid Betting Shops